Leave Your Message
In today's digital landscape, securing networks is more crucial than ever. The "Juniper SRX4600 AC" is a powerful tool for achieving this. Renowned expert Dr. Emily Chen, a cybersecurity specialist, once said, "Configuring the Juniper SRX4600 AC properly can make all the difference in preventing breaches." This highlights the importance of meticulous configuration.
The "Juniper SRX4600 AC" is designed for optimal performance and security. Yet, without proper setup, its capabilities may not be fully utilized. Many users underestimate potential vulnerabilities. A misconfigured device can lead to significant risks. Therefore, understanding the configuration process is vital for organizations.
An effective approach involves both technical skills and strategic thinking. Users must be aware of their specific network needs. Each configuration choice can impact security and efficiency. The "Juniper SRX4600 AC" demands careful consideration and continuous oversight. As threats evolve, so must our defenses. Regular updates and reviews are essential. Emphasizing the importance of these practices can significantly enhance network security.

The Juniper SRX4600 AC stands out for its robust security features. It provides a multi-layered approach to network protection. This device integrates advanced threat intelligence with a user-friendly interface. One key feature is its application visibility and control. This allows administrators to monitor and manage applications effectively.
Another essential aspect is the automated response to threats. The SRX4600 AC has tools for real-time analysis and quick action. This reduces the window of vulnerability significantly. Deep packet inspection ensures comprehensive analysis of incoming and outgoing traffic. This feature often helps in detecting hidden threats.
Tip: Regular updates of security protocols are vital. Ensure the firmware is current to protect against recent vulnerabilities.
Moreover, the ability to segment networks enhances security. Isolating critical assets helps safeguard sensitive data. However, proper configuration is essential. Missteps can lead to unintended exposure of resources.
Tip: Conduct routine audits to assess the effectiveness of security measures. This practice identifies weaknesses in real-time.
By understanding these features, organizations can harness the full potential of the Juniper SRX4600 AC.
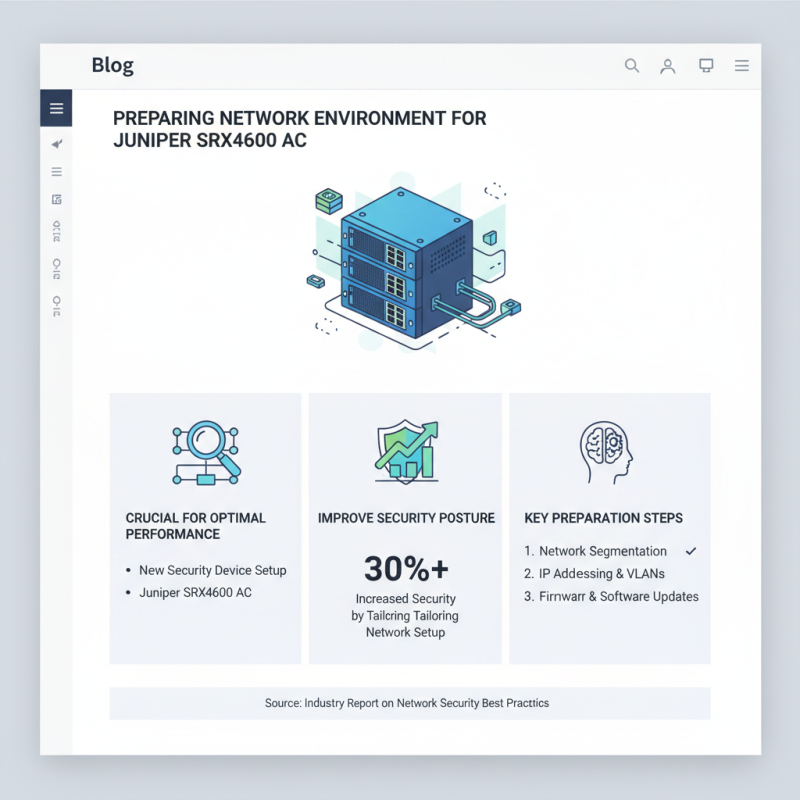
Preparing the network environment for configuring a new security device is crucial for optimal performance. The Juniper SRX4600 AC is no exception. According to a recent industry report, organizations that tailor their network setup for devices like the SRX4600 improve their security posture by over 30%.
Start by assessing your current network layout. Identify potential bottlenecks and weak points. Ensure your bandwidth is adequate for the expected traffic flow. A congested network can severely impact the SRX4600's performance. Properly segment your network into manageable sections. This helps to isolate security threats effectively.
Tip: Utilize VLANs to segregate different types of traffic. This simple step can enhance security and performance. Additionally, keep in mind that even well-configured devices may still face challenges. Regularly review and update your firewall rules to prevent obsolescence.
Monitor your environment continuously. The dynamic nature of threats means what works today may not be effective tomorrow. A staggering 75% of businesses report facing evolving cybersecurity threats. Tailor your response according to real-time data.
Tip: Implement logging on the SRX4600 for continuous visibility. This can assist in identifying anomalies swiftly. Remember, even the best configurations require ongoing evaluation and adjustment.
Configuring the SRX4600 AC for optimal network security involves several important steps. Start by accessing the device through a console cable. You will need to log in using default credentials. This initial access is critical. Set a new admin password to enhance security. Next, define the device's hostname. A unique name helps in network identification and management.
Once logged in, it’s vital to configure the basic network settings. Assign interfaces to the appropriate security zones. Ensure that public and private traffic is separated. This separation reduces exposure to potential threats. Another essential step is enabling network address translation (NAT) for outbound traffic. This adds a layer of obfuscation that can deter outsiders.
Regularly review the configuration for vulnerabilities or misconfigurations. This practice helps uncover areas for improvement. Monitor logs consistently to catch unusual activities. Security is not a one-time setup. Continuous adjustments are necessary. Reflect on the changes made and their impacts on overall security. This is a learning process, and flexibility is key.
| Configuration Step | Description | Estimated Duration | Recommended Tools |
|---|---|---|---|
| Access Device | Connect to the SRX4600 AC via console or SSH. | 5-10 minutes | Terminal Emulator |
| Initial Setup | Configure basic settings such as hostname, time zone, and interfaces. | 15-30 minutes | Web Interface / CLI |
| Security Policies | Create security policies for traffic control and management. | 30-45 minutes | Policy Management Tool |
| NAT Configuration | Set up Network Address Translation for internal and external communication. | 20-30 minutes | Configuration Guide |
| Monitoring | Enable logging and monitor traffic for anomalies. | 10-20 minutes | Monitoring Tools |
Implementing advanced security policies on the Juniper SRX4600 AC requires a strategic approach. According to the latest cybersecurity report by a leading industry analyst, 43% of companies that experience a data breach do not recover. Thus, organizations must prioritize robust security policies. The SRX4600 AC, known for its integrated threat intelligence, can significantly enhance overall network defense when configured correctly.
To create effective security policies, start by defining clear rules based on your organization's specific needs. Analyze traffic patterns and identify potential vulnerabilities. Utilizing features like application visibility and control can aid in this assessment. Furthermore, ensure that your security rules are regularly updated to adapt to emerging threats. In a 2022 survey, 79% of organizations indicated that outdated configurations were a significant factor in security incidents. Ignoring these updates can leave your network exposed.
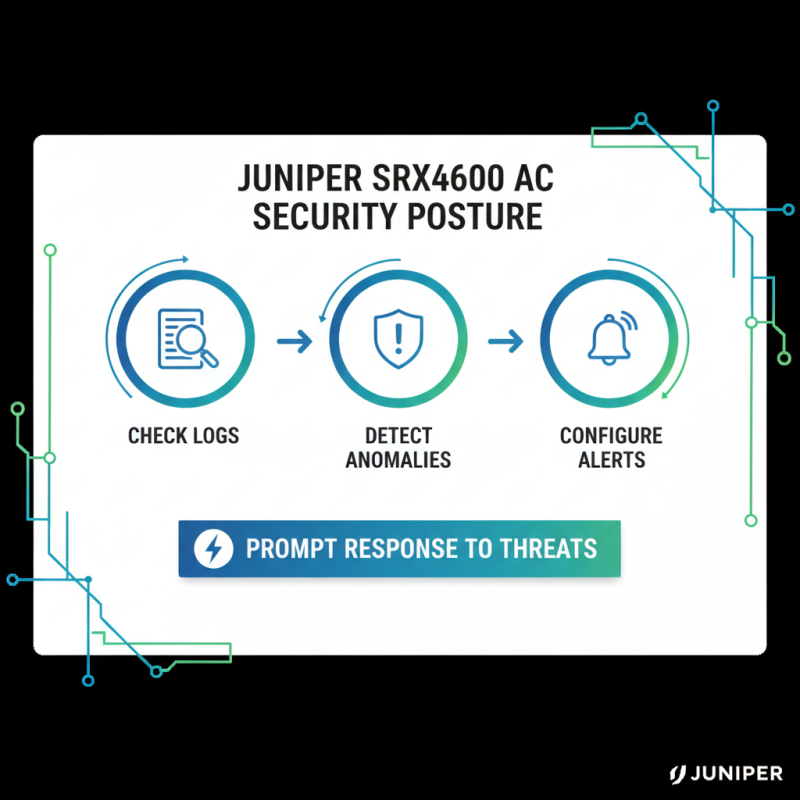
Monitoring the security posture of a Juniper SRX4600 AC requires a systematic approach. Regularly check the logs for unusual activities. Intrusions can often be detected through anomalies in log files. Configure alerts to notify you of any critical events. This will help in prompt response to potential threats.
Routine updates are essential for maintaining optimal security. Ensure that the firmware is current. Old firmware can have vulnerabilities that attackers exploit. Conduct security audits periodically to identify gaps. This also includes assessing the configuration changes made by network engineers.
Consider implementing automated tools for real-time monitoring. These tools can help in identifying risks before they escalate. However, manual verification is still necessary. Human oversight can catch errors that automation might miss. Mistakes in configuration can lead to increased risk, so periodic reviews are critical.






